Apple’s high security mode blocked NSO spyware, researchers say
Reading Time: 3 minutesLast year, Apple launched a new feature for iPhone users who are worried about getting targeted with sophisticated spyware, such as journalists or human rights defenders. Now, researchers say they have found evidence that the feature — called Lockdown Mode — helped block an attack by hackers using spyware made by the infamous mercenary hacking provider NSO Group.
On Tuesday, the cybersecurity and human rights research group Citizen Lab released a report analyzing three new zero-day exploits in iOS 15 and iOS 16 — meaning Apple was unaware of the vulnerabilities at the time they were used to target at least two Mexican human rights defenders.
One of those exploits was blocked by Lockdown Mode, the researchers found. Lockdown Mode was specifically designed to reduce the iPhone’s attack surface — cybersecurity lingo referring to parts of the code or features of a system prone to attacks by hackers. This is the first documented case where Lockdown Mode has successfully protected someone from a targeted attack.
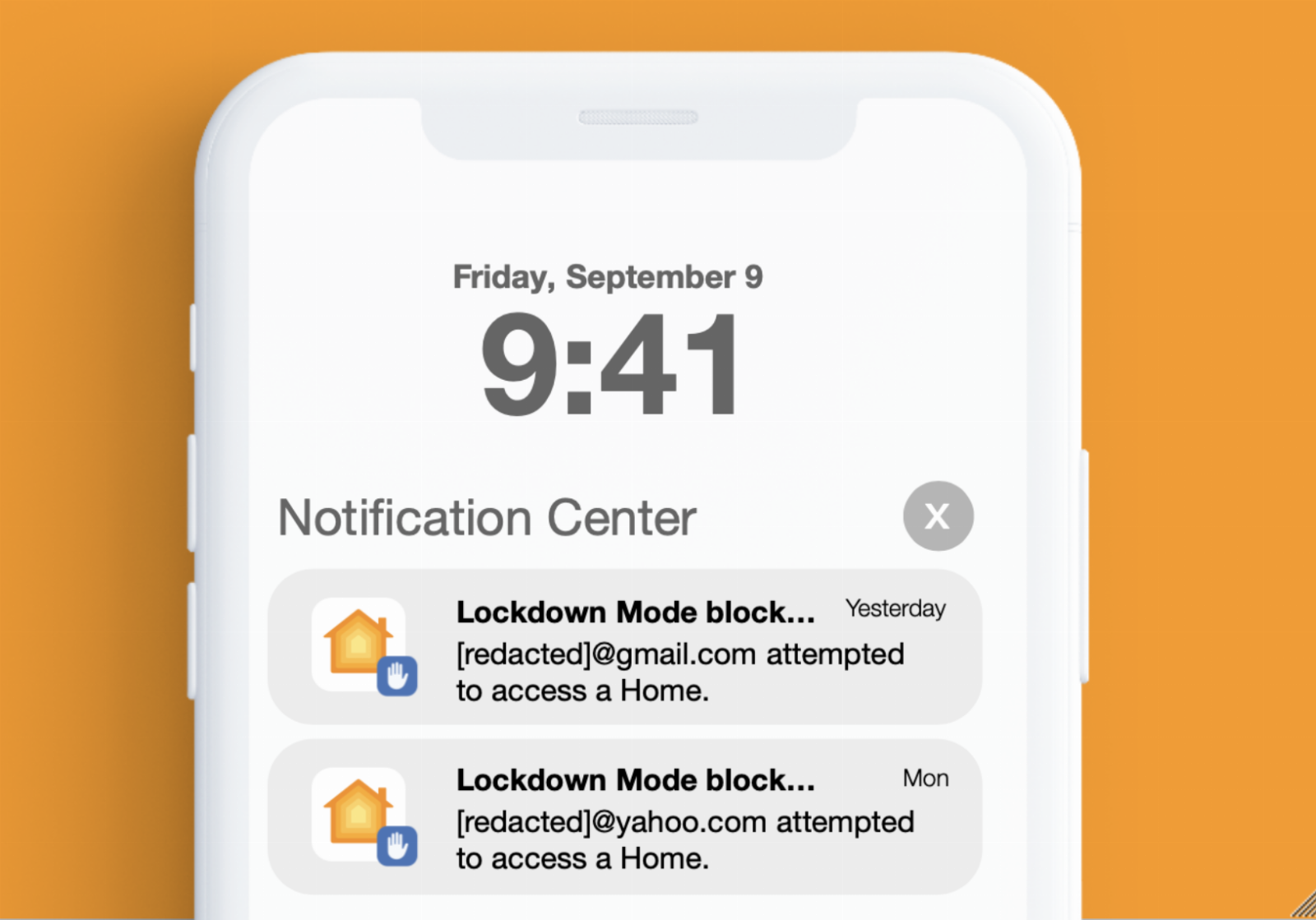
In the recent cases, Citizen Lab researchers said that the targets’ iPhones blocked the hacking attempts and showed a notification saying Lockdown Mode prevented someone from accessing the phone’s Home app. The researchers, however, note that it’s possible that at some point NSO’s exploit developers ‘may have figured out a way to correct the notification issue, such as by fingerprinting Lockdown Mode.’
As other researchers have pointed out in the past, it’s easy to fingerprint users to determine who has Lockdown Mode turned on, but that’s not to say its protections are not meaningful. As this case found by Citizen Lab shows, Lockdown Mode can be effective.
Apple spokesperson Scott Radcliffe said in a statement: ‘We are pleased to see that Lockdown Mode disrupted this sophisticated attack and alerted users immediately, even before the specific threat was known to Apple and security researchers. Our security teams around the world will continue to work tirelessly to advance Lockdown Mode and strengthen the security and privacy protections in iOS.’
NSO Group spokesperson Liron Bruck did not respond to a series of questions, instead sending a statement saying that ‘Citizen Lab has repeatedly produced reports that are unable to determine the technology in use and they refuse to share their underlying data. NSO adheres to strict regulation and its technology is used by its governmental customers to fight terror and crime around the world.’
Citizen Lab’s report identified three different exploits — all ‘zero-click,’ meaning they did not require any interaction by the target — by analyzing several phones that were suspected to have been hacked with NSO’s spyware, also known as Pegasus.
Pegasus, which NSO sells exclusively to government customers, can remotely obtain a phone’s location, messages, photos, and virtually anything the phone’s legitimate owner can access. For years, researchers at Citizen Lab, Amnesty International and other organizations have documented several cases where NSO customers used the company’s spyware to target journalists, human rights defenders, and opposition politicians.
Citizen Lab’s new findings show that NSO is still alive and well, despite a rocky past couple of years. In 2021, an international consortium of media organizations launched the Pegasus Project, a series of articles detailing scandals involving NSO all over the world. Then, later that year, the U.S. government put NSO on a denylist, effectively barring any U.S. company or individual from doing business with the company.
‘Other companies have folded, but, at least for now, NSO is still able to bear these increased costs, and Pegasus remains an active threat to global civil society,’ Marczak said.
Of the recent batch of exploits: the first exploit was deployed in January 2022 by NSO customers and exploited the iPhone’s FindMy feature, which helps owners locate their lost or stolen phones. The second exploit deployed starting in June 2022 and is a ‘two-step’ exploit, meaning it targets two features, in this case the FindMy feature and iMessage. And the last exploit, deployed starting in October 2022 exploited the iPhone’s HomeKit and iMessage functionalities.
In its report, Citizen Lab said the two Mexicans targeted by the exploits investigate human rights violations allegedly carried out by the Mexican military. The Mexican government is a known spyware customer.
Citizen Lab reported all these exploits to Apple, which have since then pushed updates and reduced the attack surface. Apple fixed the HomeKit-based vulnerability in iOS 16.3.1, released in February.
Reference: https://techcrunch.com/2023/04/18/apple-lockdown-mode-iphone-nso-pegasus/
Ref: techcrunch
MediaDownloader.net -> Free Online Video Downloader, Download Any Video From YouTube, VK, Vimeo, Twitter, Twitch, Tumblr, Tiktok, Telegram, TED, Streamable, Soundcloud, Snapchat, Share, Rumble, Reddit, PuhuTV, Pinterest, Periscope, Ok.ru, MxTakatak, Mixcloud, Mashable, LinkedIn, Likee, Kwai, Izlesene, Instagram, Imgur, IMDB, Ifunny, Gaana, Flickr, Febspot, Facebook, ESPN, Douyin, Dailymotion, Buzzfeed, BluTV, Blogger, Bitchute, Bilibili, Bandcamp, Akıllı, 9GAG